Drexel Libraries Celebrates Cybersecurity Month with ScholarSnack Event on Ethical Hacking
November 2, 2018
On Wednesday, October 24, sixty Drexel students, faculty and staff filled two classrooms in the W. W. Hagerty Library to participate in a special ScholarSnack workshop: An Introduction to Ethical Hacking of Internet of Things (IoT) Devices.
Thomas Heverin, PhD, Teaching Professor at the College of Computing and Informatics, lead the workshop, which drew a mix of computer science students and faculty, as well as students from other disciplines like engineering and public health.
Dr. Heverin began the session with an introduction to the key concepts of cybersecurity and ethical hacking, issues that apply to both corporations and the average person.
“Everyone needs to be concerned with their online safety,” explained Dr. Heverin, who teaches Computing and Security Technology courses at Drexel. “The average person doesn’t always think to put a password on home devices, like webcams. But if you don’t protect your devices, hackers can remotely? find and access them online—they could watch your home through your own webcam. Cybersecurity isn’t just for big corporations.”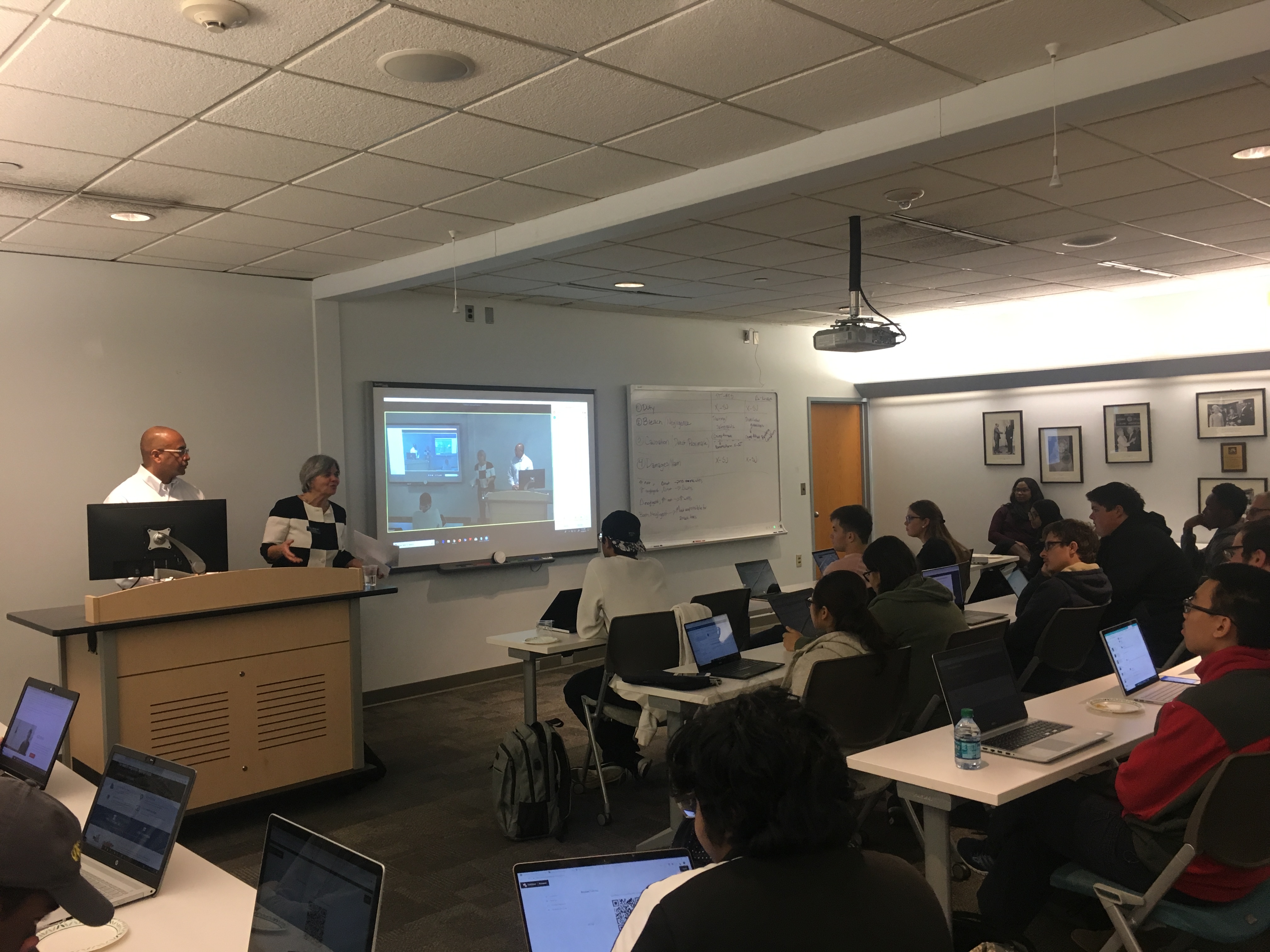
But hacking isn’t always malicious. Dr. Heverin (who is a Navy veteran and a defense contractor in cybersecurity and artificial intelligence) also described what’s called ethical hacking—evaluating the security of and identifying weaknesses in a computer or network system to determine whether unauthorized access or other malicious activities are possible. Ethical hackers are information security experts who attempt to penetrate computing resources on behalf of their owners—and with their permission—to find and fix security vulnerabilities a hacker could potentially exploit.
“Ethics is a big part of cybersecurity,” Dr. Heverin stressed during the workshop. “Just because you can access a device, doesn’t mean you should. It’s illegal to access and change settings on devices and networks without permission, so unless someone gives you the go-ahead, don’t touch it. This is so important to remember.”
For the second half of the event, Dr. Heverin demonstrated how to use the online search engine Shodan to perform reconnaissance, the first stage of ethical hacking. He noted that using search engines like Shodan to do reconnaissance is perfectly legal, and all information on the website is publicly available. But actually accessing and altering things on those devices, he warned, can lead to legal trouble.
During reconnaissance, security experts attempt to gather as much information about a target system as possible, like determining the network range, or discovering open ports and access points.
Reconnaissance requires detective work and critical thinking. Many of the information-gathering skills students perfect using the Drexel Libraries’ resources for research and coursework are necessary skills for cybersecurity experts.
“So much of cybersecurity work is searching for and gathering information,” Dr. Heverin told attendees. “The use the same skills librarians encourage in utilizing the Drexel Libraries’ resources, like the how to find and evaluate information for research papers or course work. Those skills are so important for cybersecurity professionals. For example, you might have to look at information like IP addresses to understand and learn more about a device. You may need to search other websites or use different search engines to put together the pieces of the puzzle and to understand what type of device you’re looking at and what its vulnerabilities are. It’s not all spelled out for you on the page.”
The workshop was organized by the Drexel Libraries and the College of Computing & Informatics (CCI) as part of National Cybersecurity Awareness Month (NCAM). NCAM is an annual initiative to raise awareness about the importance of cybersecurity.